Share This Post
As a long-time WordPress user, I was surprised to learn that I was inadvertently weakening my WordPress username security through a default function, the Author URL (Uniform Resource Locator, or, to put it simply, the website address). Essentially, I was advertising my creative username AND Google was picking it up to share with the world.
Are you making the same mistake? Simple test. Go to Google.com and enter in the search box yourwebsitename/author/ and check the results. Is your username showing up in one of the search results? Even if your username is not the “displayed” choice in your WordPress options?
In this post, I will explain what is happening and show you in a few simple steps how to fix the issue.
Who Would Hack My Site?
Your website is just about your family, your dogs, your cats, your vacation photos, whatever – who would try to hack it?
I thought the exact same thing in my early days of hobby websites. IT security was something corporations had to worry about, or small businesses using e-commerce, not me.
After one of my personal websites outgrew the capabilities of a shared hosting environment, I moved it to a VPS. Unlike a shared hosting environment, I was now responsible for security on that machine, so had basic security measures to prevent multiples login attempts. What I quickly discovered was that I was seeing unauthorized login attempts multiple times every day. Sometimes, I would see bursts of multiple attempts a minute.
Looking back at the shared hosting environment, I was seeing the same types of attempts. I had just never noticed before. (Do you check your security logs regularly? I do now.)
So, yes, someone probably has attempted to hack your site. They don’t care about your data. They care about access to another website to go about their malicious work.
Background
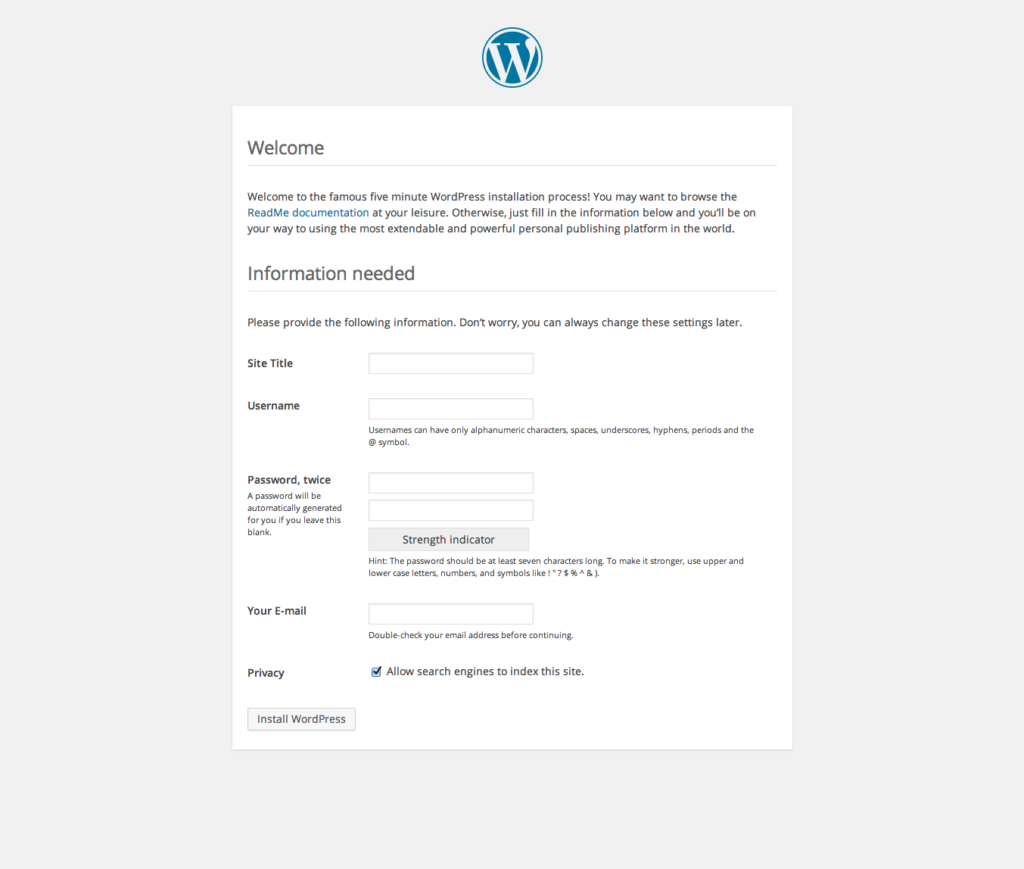
Let me define the issue about WordPress username security. When you initially set up WordPress software, you are greeted with the following screen:
Of this information, only the Site Title should be widely known. After all, the title is a key part of your SEO in attracting website traffic.
You want to keep your username, your email address and your password secret because those are the keys to logging into your website. If someone knows your username and password OR your email address and password, they can just log in.
So let’s look at the three pieces of the puzzle.
Password
A strong password is your foundation. Even if your username or email address are known, a strong password can slow down hack attempts.
But let’s talk strong.
- Are you using both upper and lower case letters? Numbers? Symbols?
- How long is your password? At least twenty characters?
- How often do you change your password?
- Is this password used anywhere else?
I know, I know, how can you be expected to remember such a password? And so many of them? The answer is simple – you don’t. There are so many tools out there today like 1Password, Dashlane, and LastPass which can manage your passwords. And since they can generate random passwords for you, no chance of falling into a pattern of “guessable” passwords.
And that fourth bullet point about using the same password in more than one place? A common hacking technique is to capture usernames and passwords from one place and try the combination in other places – like your bank. Seriously, if you learn nothing else from this post, go change your banking password(s) right now if they are the same as any other website you use. Please.
Username
Good. You have a strong password in place. For many people, that will be enough. But if you make your username equally difficult to guess, your security has grown exponentially. In a brute force attack, the hacker will enter your known username and then random characters to guess your password. If they have to guess a complex username AND a complex password, the number of potential combinations grows to such a large number that they are more likely to move on to a less secure (or more valuable) target.
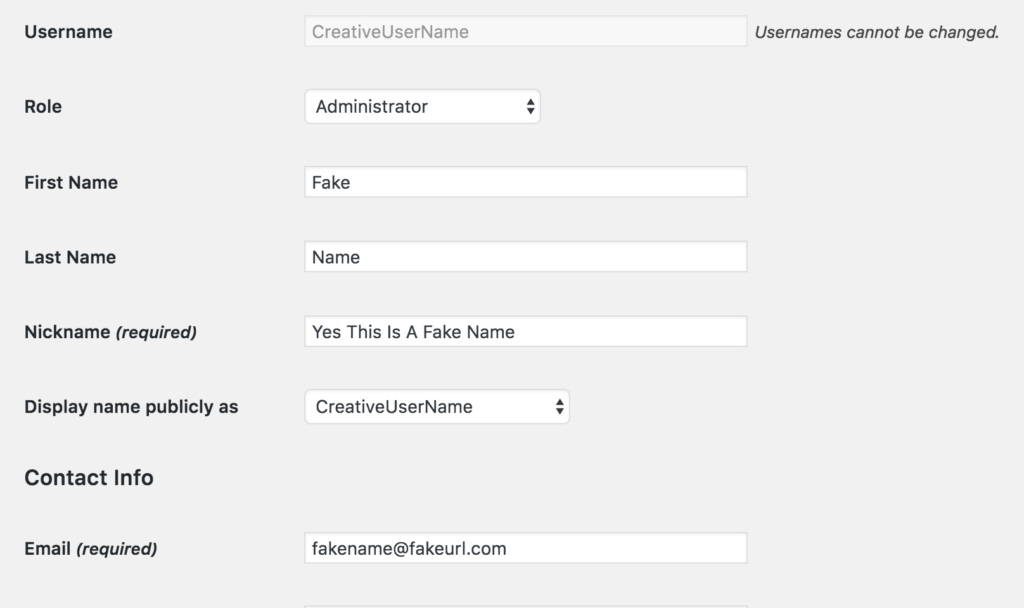
As we showed above, when you create WordPress or add a new user, you add a username, email address and password. If you go to the user edit screen ( Users > All Users > Edit), the result is:
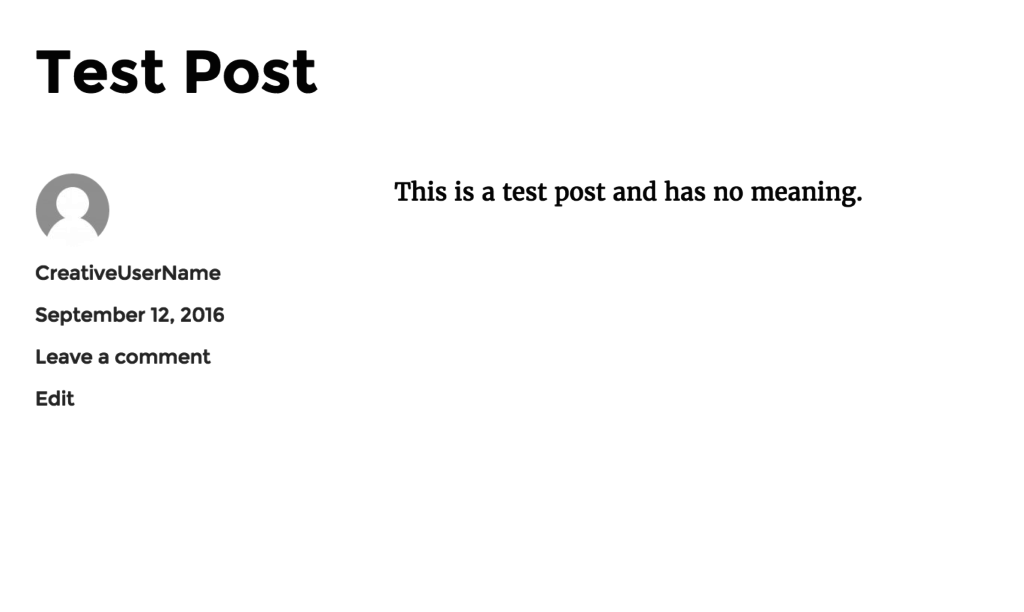
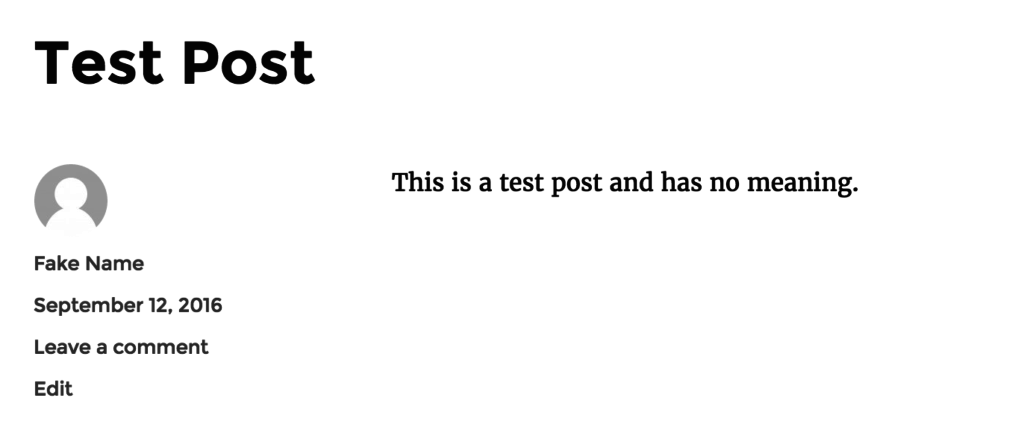
And a post would show this information:
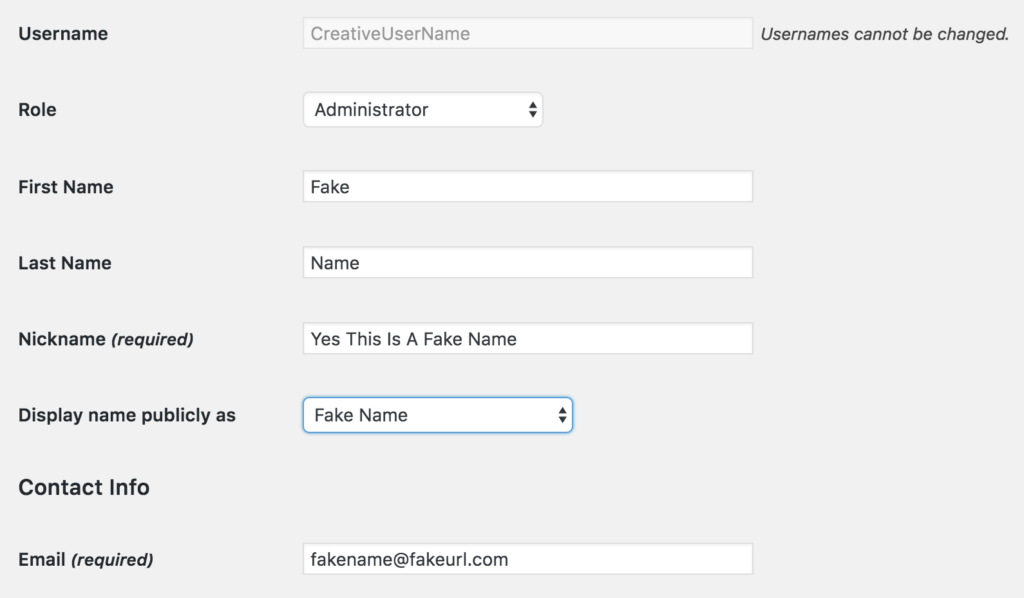
Yep, there is the user login. So, let’s make a simple change using the drop down box for “Display Name Publicly As”:
And now that blog post looks like this:
Awesome! The username is now hidden, right? I sure thought so and had operated for a long time with that confidence. One day, though, I was reviewing my Google Analytics data and noticed that my creative username was being publicly revealed by WordPress in an URL.
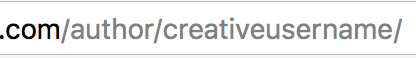
To demonstrate, perform a very simple test. In that post, click where the author’s name appears and you will discover it take you to an “author” page that shows all posts by that author. Now check out the URL in your web browser:
Yep, that’s right. WordPress automatically displays the username in the URL. And notice in the user edit screen that there is no field for changing that.
There are several ways to fix this via plugins and PHP programming, but the real issue here is simple – it’s a database issue. While you rarely want to reach into your database and make changes (horrific things can happen), this is a case where the cleanest fix is right there in the database. No need to add lines of PHP code when a simple fix of the data solves the problem quickly and easily.
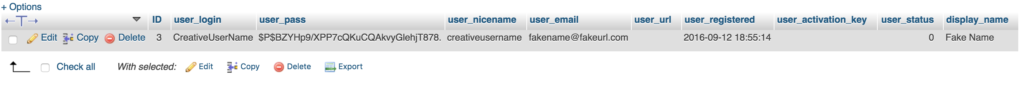
Go to your database via whatever tool you use (the screen shot is from PHPMyAdmin) and find the users section. You should see something like this:
Notice the “user_nicename” field? Edit that one field to a more acceptable field and save:
Go back and reload your posts page, click on the author’s name. Everything will look exactly the same except for the URL:
And now your username is truly hidden.
How Complex a Username
Thanks to the password programs that I mentioned earlier, your usernames can now be as complex as your password. I now use randomly generated usernames in addition to randomly generated passwords.
Email Address
One last issue. Starting in WordPress 4.5, the ability to login via your email address was added. In my opinion, the problem is that email addresses are easier to figure out than usernames. All of that work we did above has been negated by allowing a simple email address to be used.
One solution is to use an obscure email address that is not used for any other purpose, but it would still need to be a legitimate email address. And that means you would have to create and maintain another email address. Since I run my own mailserver, that is not too bad for me, but I think most people would find that far too complicated and not worth the effort.
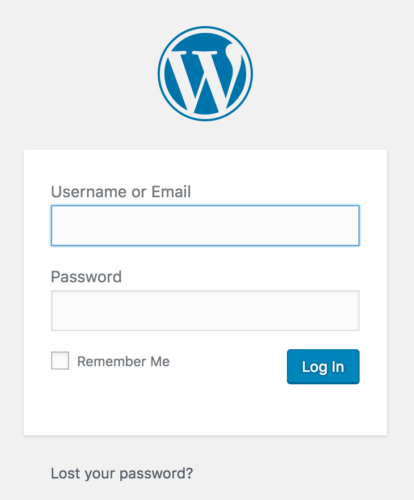
In this case, the easier suggestion is to simply remove the email address as an option via PHP. Being open source software, a simple answer has already been introduced via the “No Login By Email Address” plugin. Install that and your login screen now looks like:
Do I Really Need To Hide All Of My Usernames?
For the most security, sure, but where is the real risk? The real risk exists in users with Administrator Rights. If you allow others to sign in to your WordPress site, make sure you are using user roles levels and give them just the access they need. The risk of someone hacking an author user account is only in what they can publish, a fairly easy problem to fix. If someone hacks an administrator account, they can lock you out. (Well, until you go into the database, but that is a different post.
Keep the number of administrators to a minimum number.
Limiting Login Attempts
Though this is beyond the scope of this post, the other piece of the security puzzle is to limit the number of times someone can attempt to login. This greatly reduces the power of brute force attacks because a hacker can only make so many guesses before being locked out.
If you are using WordPress in a hosted environment, you may not have access to the operating system. In that case, you need to lock things at the WordPress level. There are several plugin options – many with advanced features like Sucuri and WordFence. A simple plugin aimed at just the topic of limiting login attempts is WP Limit Login Attempts.
If you are using your own server or VPS, you can program security for the whole server using Fail2Ban or similar options.
Conclusion
As I mentioned at the outset, I only recently discovered that I was not as secure as I thought using a creative username.
The fixes as outlined above were easy to make. I thought I would take the time to share what I learned and walk you through the steps in a plain language approach.
Hope that it helps you in keeping your WordPress site secure.
Affiliate Link Disclosure
The article above contains many links, some to open source products and some to products for sale. NONE of those links are affiliate links and I do not earn a penny from any of them. Yes, you heard that right. None of them are affiliate links. Nor am I affiliated with any of these companies except as a user of their products – all of which I paid full retail price for. I have received no consideration for mentioning any of the products.